Strategic Expansion Tactics in a Contracting Economy
In the face of economic downturns, the prospect of expanding a company may seem counterintuitive. However, history reveals that successful enterprises often emerge during challenging times. Disney, Hewlett-Packard, Netflix, Citigroup, Groupon, and Lego all thrived during economic recessions, underscoring the potential for growth amid adversity. In this blog post, we’ll explore the key considerations when expanding to a new location during an economic downturn and how to effectively mitigate associated liabilities.
1. Identify and Manage Risks
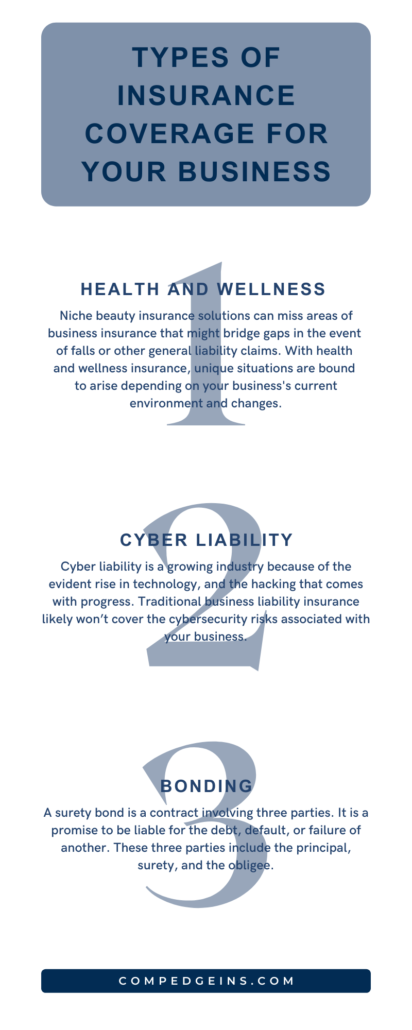
Every expansion comes with its own risks, including property damage, liability claims, and business interruption. Consider working closely with your insurance provider to identify any liabilities related with the relocation site. A customized insurance policy can give financial protection against unforeseen obstacles, allowing your company to navigate uncertainty with greater confidence.
2. Review and Adapt Contracts
Before expanding, thoroughly examine your contracts for the new location. Ensure that your agreements align with the local regulations and economic conditions. Early contract adjustments can prevent legal complications and financial penalties, providing a solid foundation for your operations.
3. Prioritize Employee Well-being and Benefits
The talent and well-being of your team are critical to the success of any expansion. Consider offering comprehensive employee benefits and risk management programs to safeguard your team’s health and safety. This not only fosters a positive workplace culture, but it also protects your company from potential liability originating from workplace incidents or employee conflicts.
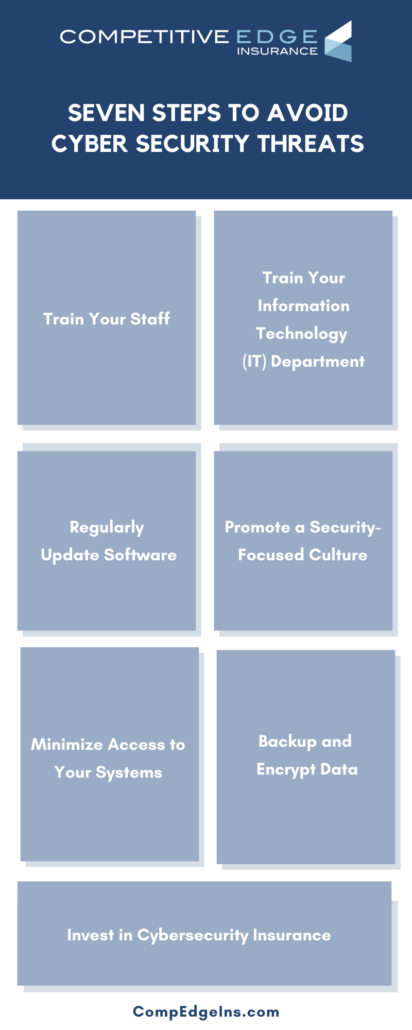
4. Invest in Cybersecurity
In the age of digital transformation, companies must emphasize cybersecurity and data protection. With the rising risk of cyber threats, make sure your company invests in strong cybersecurity procedures to protect sensitive data. Also, establish a robust IT infrastructure by assembling a dedicated IT team and conducting comprehensive training programs to ensure seamless technological integration and data security. To reduce potential financial losses, look into insurance solutions that cover cyber liabilities like as data breaches and cyber attacks.
5. Make Adjustments Early
Proactive adjustments are key to successful expansion. Waiting until the last minute can lead to complications and hinder the relocation process. Implement changes early to streamline operations, mitigate risks, and ensure a seamless transition.
6. Prioritize Employee Well-being and Benefits
The talent and well-being of your team are critical to the success of any expansion. Consider offering comprehensive employee benefits and risk management programs to safeguard your team’s health and safety. This not only fosters a positive workplace culture but also protects your company from potential liability originating from workplace incidents or employee conflicts. Expanding to a new location during a contracting economy requires careful planning, risk assessment, and strategic decision-making. By working with a reliable insurance company and implementing a comprehensive risk-management strategy, your business can not only survive but also thrive during difficult economic times. Don’t forget that proactive actions and a carefully considered insurance plan can be your company’s shield against liabilities, enabling you to expand with peace of mind and resilience.
We can help you find the best policy to provide the coverage you’ll need to bounce back if attacked.
Featured image credit: Envato Elements by Rawpixel | Licensed | All Rights Reserved